Check your forwarding rules. Email security is critical for everyone. It’s the account that controls most of your others. Need to reset a password? Or verify your identity for other reasons? You’ll probably get an email with a link. If…
Category: Security
The 10 laws of computer security
Basic principles of IT security don’t change. Microsoft published a list of 10 computer security “laws” that do not change over time. These “immutable laws” (amusingly published as version 2.0) give a good, largely non-technical shot of reality into data…
The Coming Mac Threat (Revisited)
How we viewed security for the Mac in 2008. This is a republished article from MacUser magazine. In The Coming Mac Threat (Revisited) we look at how experts perceived security for the Mac back in 2008 and how well that…
12 Security Tips (revisited for 2021)
We look at how security advice has evolved in 6 years. How much has computer security changed in the last six years? In 2015, six years ago to the day, I published a 12-point security tips list. The goal was to…
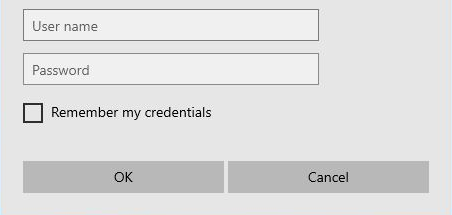
Windows Security wants your Outlook password (over and over) – SOLVED
Scenario: Outlook on your Windows 10 PC has stopped working, continually asks for your username and password, but nothing you type will work. You’ve tried Googling it. Your Outlook password isn’t working! There is lots of advice about resetting Profiles,…
Back up Windows 10 to an encrypted drive more easily
Back up your data to an encrypted external disk for free – money-free and hassle-free. Summary: use auto-unlock so you don’t need to enter your drive’s encryption password every time you use it. Backing up your data has always been…
Certified insane: Anti-malware certifications
Are anti-malware certifications fluff, perfect or basic hygiene ratings? Nearly ten years ago I wrote an article for Computer Shopper magazine about anti-virus (aka anti-malware) certifications. The words, along with my website, have long since shuffled off into archive.org. Here’s a…
How was Hacking Team hacked?
The attacker who stole Hacking Team’s data gained access to an employee’s computer while the victim was still logged in. The attacker either had direct physical access to Christian Pozzi’s PC or they used malware to achieve a similar level…
12 Computer Security Tips
Quick and easy (but expert) guide to computer security. The bad guys can try to break in using computers only or they can try to trick you into providing them with access. Or they can use a mixture of tactics.…
Password reset accessibility hack
You’ve forgotten your Windows password. What now? (Part two of Three ways to recover from a forgotten Windows password.) Hack to reset your password(s)… Windows provides accessibility tools at the login screen when the user pressing the Shift key five…